Critical Android flaw can be used to hack almost any phone: What to do
Critical Android flaw can be used to hack almost whatever phone: What to practice

If your Android phone tin install Google's May security update, make sure you run the update.
A critical vulnerability chosen Strandhogg 2.0 revealed yesterday (May 26) tin can be used to "proceeds access to private SMS messages and photos, steal victims' login credentials, track GPS movements, make and/or record phone conversations and spy through a telephone's photographic camera and microphone," according to the flaw's finders at Norwegian app-security firm Promon.
- The all-time Android antivirus apps to keep your smartphone safety
- All-time Android phones of this yr so far
- Latest: OnePlus Z could soon boxing Google Pixel 4a
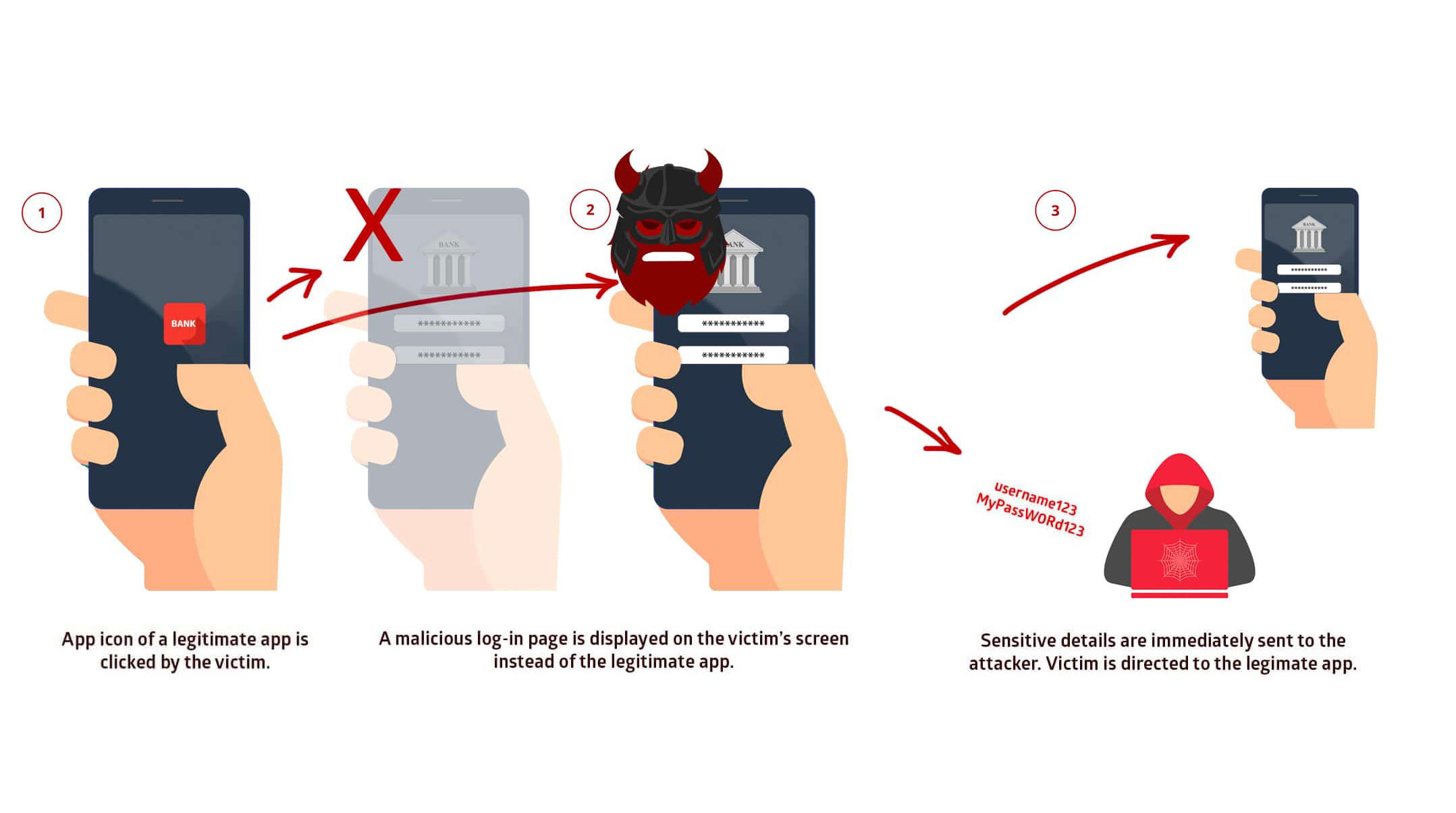
Strandhogg 2.0 superficially resembles the before Strandhogg Android flaw that Promon disclosed in Dec 2019. Both Strandhoggs (the name comes from a Viking term for embankment raids) allow malware spoof legitimate Android apps and system screens.
As a event, you might blazon your Facebook username and password into a simulated Facebook app rather than the real matter, handing command of your Facebook account over to attackers (unless you accept two-factor authentication activated). Or you could give an attacking app permission to use your camera and microphone, letting information technology spy on you.
Who is (and isn't) vulnerable to Strandhogg 2.0
The good news is that Android ten phones are immune from Strandhogg 2.0, and that Android 8.0 and 8.ane Oreo and Android nine Pie were patched with security updates at the beginning of May. The flaw has also non withal been exploited in the wild, although that may alter before long.
The bad news is that many phones that aren't Google Pixels or Samsung flagships will not get the May security patch for several months. Older phones running earlier versions of Android will probably never exist patched.
Both versions of Strandhogg tin be driveling without taking whatever app permissions, and then there would be very little to tip off the phone user that something might be amiss. However, the start Strandhogg is easy to detect using Google's own Play Protect software.
Not so with Strandhogg ii.0. Malware exploiting it might canvas by even the best Android antivirus apps. Perfectly innocuous apps might afterwards exist updated to exploit Strandhogg 2.0, fooling Google Play.
Promon researchers notified Google of the Strandhogg ii.0 flaw on Dec. iv, 2019, and Google confirmed the severity of the flaw 5 days later. Still, information technology took Google nearly five months to fix the vulnerability, and Promon cut Google a break by extending its 90-day disclosure deadline by an extra month twice.
Source: https://www.tomsguide.com/news/android-strandhogg2-flaw
Posted by: rosathesert.blogspot.com


0 Response to "Critical Android flaw can be used to hack almost any phone: What to do"
Post a Comment